Multi-Factor Authentication for Active Directory Federation Services 3.0 (ADFS 3.0)

A critical capability of a Next-Gen Access management service is the ability to protect applications and data by ensuring high levels of Authentication Assurance. Authentication to a system is about proving the user’s identity to the system – in essence, proving that the user is indeed who the user claims to be.
Authentication Assurance focuses on answering the basic question, “How sure is the system of the user is who the user claims to be?” The National Institute of Standards and Technology (NIST) Special Publication 800.63 lays out a suite of standards, guidelines and requirements that federal agencies can use to implement digital identity services. Of these guidelines, the standard 800.63b focuses on Authentication and Lifecycle Management and defines the levels and requirements associated with Authentication Assurance. These guidelines have also been the foundation of Idaptive’s industry and market leading Adaptive Multi-Factor Authentication (MFA) capabilities.
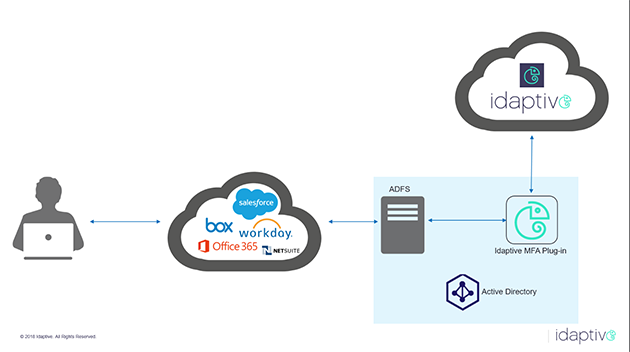
Idaptive’s MFA Everywhere strategy aims to support all enforcement points for MFA, including all types of applications, endpoints, virtual desktops, servers, virtual private networks (VPN) and such. Consequently, the latest release of Idaptive expands on this strategy further and now integrates with Active Directory Federation Services (ADFS) 3.0 for MFA. ADFS customers looking to implement higher authentication assurance levels for their users as they federate into applications through ADFS can now use Idaptive’s AFDS plug-in to turn on MFA for those users. A high-level overview of the architecture is below.
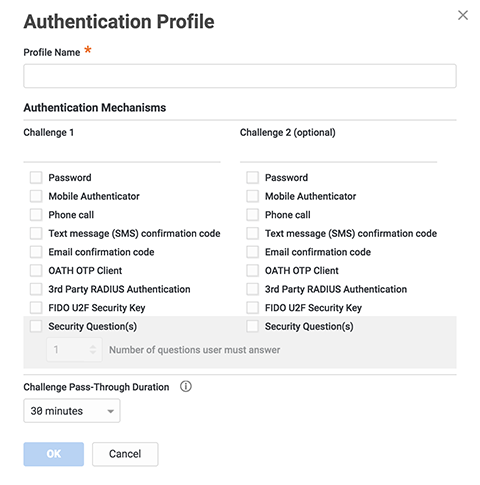
Idaptive’s ADFS MFA plug-in supports all the authentication factors currently supported within Idaptive. These include a one-time password delivered over SMS or email, OATH OTP codes, Security Questions (challenge/response) among others. The screenshot below shows all the authentication factors supported within Idaptive’s Authentication Profiles capability.
To download this plug-in and install it in your ADFS deployment, please visit the Idaptive GitHub page here. The page includes the plug-in software as well as a detailed installation, configuration, and uninstallation manual. We’d love to hear your feedback!


