Building the Next Generation of Identity and Access
Complexity is the enemy of Efficiency.
Unnecessary barriers can kill a team’s productivity, doom an app or program to failure, or render collaboration ineffective, unfriendly and counterproductive. In security – especially identity and access – complexity introduces risk.
When organizations start to look at how they can put a Zero Trust security strategy in place, one of the first things they notice is that it can be complicated. How does a CSO implement a strategy that presumes that users and endpoints are not trustworthy and must be verified without turning to a cacophony of different vendors, solutions and integrations?
This is where next-gen access comes into play.
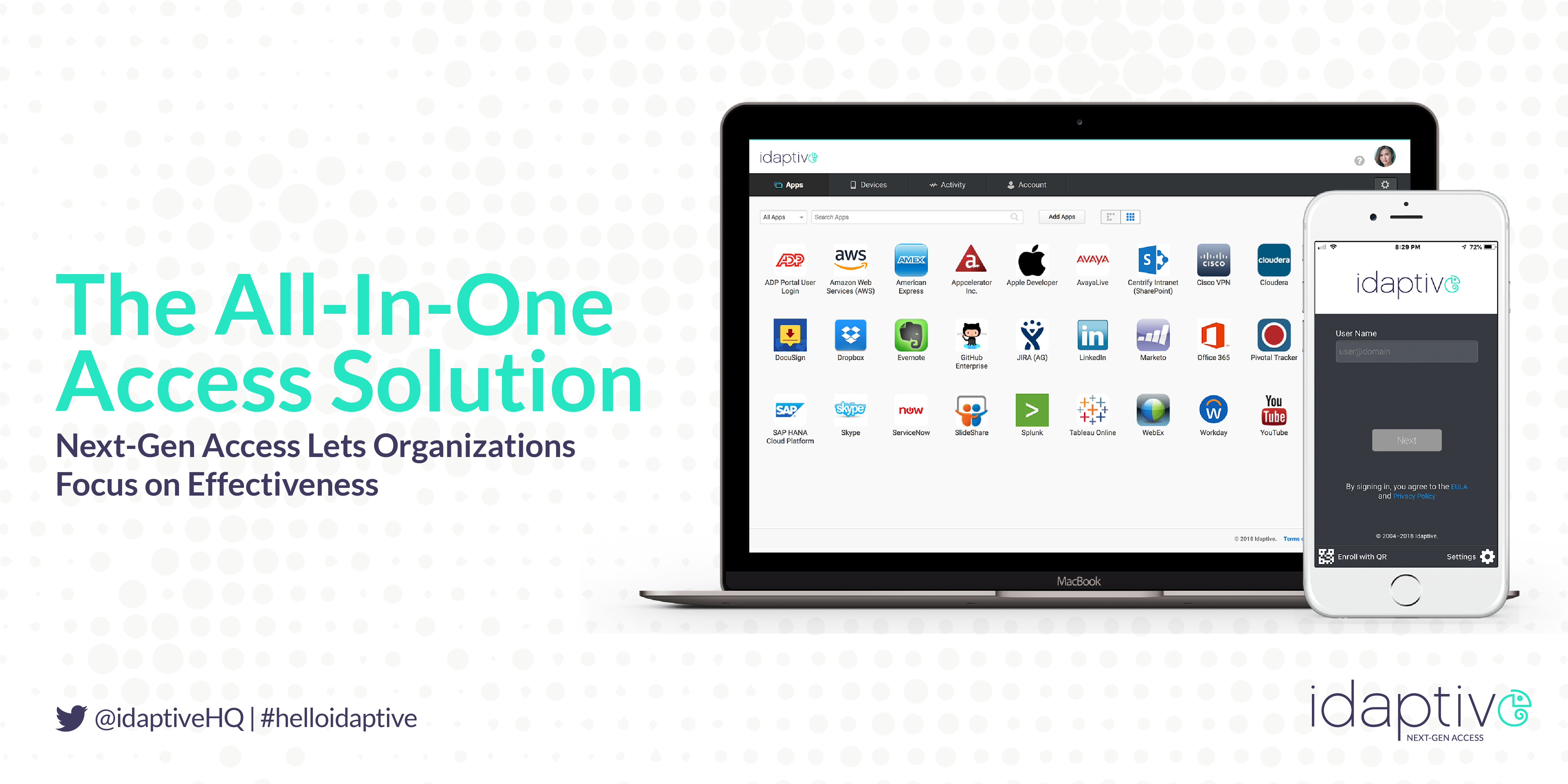
The All-In-One Access Solution
Next-gen access does all this by converging single sign-on (SSO), adaptive multi-factor authentication (MFA), workflow and lifecycle management, enterprise mobility management (EMM) and user behavior analytics into one platform, providing effective security without performance gaps and difficult integrations and maintenance.
Next-gen access solutions are better equipped to enable a Zero Trust approach to access, with advanced capabilities that intelligently determine the authenticity of a digital user and their device, governs access across an organization’s resources, and reacts when risky behavior is detected. This bolsters an organization’s security posture while also improving end user experiences, making everyone more productive.
A Careful Balance of Security and User Experience
For too many years, access control technologies have been about putting additional layers, barriers and friction into the user’s path in the hopes of deterring a bad guy. (Remember those awful RSA hard tokens with no backlight and no replaceable battery?) This conflicts with the reality that 99 percent of the time, users are who they say they are, doing what they are supposed to be doing. So how do we continue to improve access control security – which is the top vector of attack by far, with 81 percent of breaches involving weak or stolen passwords – while balancing with a great user experience?
The key is finding a balance between the two that elevates the security of every access attempt while at the same time reducing friction for end users and the burden on IT. Next-gen access solutions can use analytics powered by machine learning to intelligently determine the authenticity of a digital user and their device through SSO or MFA, while also actively governing access across an organization’s resources, and reacting when risky behavior is detected.
This cuts down on friction for the user, who is just logging in as they always do, while enforcing Zero Trust policies.
Psst: It Saves Money Too
Most people think about security solutions as ways to avoid the cost of a breach, comply with regulations or to replace legacy technologies – bottom-line arguments that reduce or avoid security-related costs. Forrester research (“Stop the Breach”, 2017) shows that companies with a “mature” adoption of identity and access best practices report experiencing 50 percent fewer breaches than their less mature counterparts. Additionally, those that adopt a next-gen access approach report spending 40 percent less on technology, likely due to the reduction of integration, implementation, and administration costs.
But there are also real, tangible top line benefits that help growth and competitiveness. For example, another recent Forrester report (“Adopt Next-Gen Access to Power your Zero Trust Strategy”, 2018) finds that companies that implement next-gen access solutions are more than twice as confident in adopting new business models and accelerating new customer experiences to market. Another study by Ponemon shows that avoiding a breach protects shareholder value and protects from customer churn (31% of customers notified of a breach stated their intent to discontinue doing business with the notifying company).
Why Take the Hard Road?
People like things that are easy and that also work – it’s a pretty basic piece of human nature. When paired with a Zero Trust approach, next-gen access provides security teams with both, ensuring that data, systems and apps are protected, while giving users a great experience.


