Introducing the New Mac Cloud Agent
The new Idaptive Mac Cloud Agent makes it easy for you to deploy Mac devices to remote employees, ensure that devices have the right set of security policies, and are protected with Multi-Factor Authentication.

In my previous blog post, I wrote about the ways our new Windows Cloud Agent addresses the identity and access management challenges that come with the shift to the cloud-based infrastructure and distributed workforce. This week, I am excited to introduce you to the new Idaptive Mac Cloud Agent extends the benefits of cloud-centric identity management to organizations with large deployments of macOS devices. The new Idaptive Mac Cloud Agent makes it easy for you to deploy Mac devices to remote employees, ensure that devices have the right set of security policies, and are protected with Multi-Factor Authentication.

In this blog post, I will help you get started with the new Mac Cloud Agent by answering three main questions:
- What benefits does Mac Cloud Agent provide?
- What are the key features of Mac Cloud Agent?
- How do I get started?
1. What benefits does Mac Cloud Agent provide?
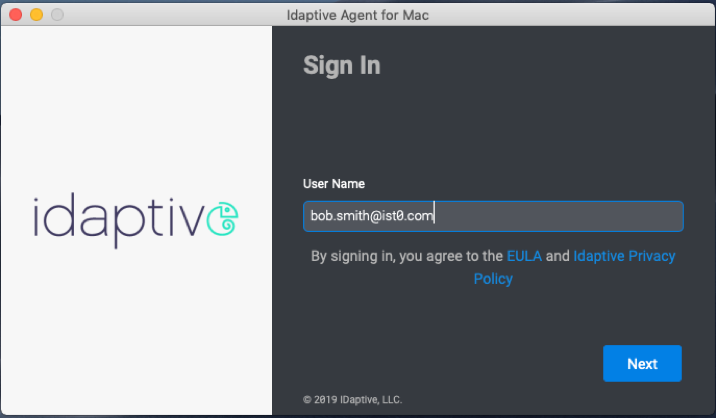
The Idaptive Mac Cloud Agent connects all of your Mac endpoints to the Idaptive platform so that your local and remote users can seamlessly sign in to their devices with their Active Directory or Idaptive Cloud Directory credentials. Previously, the process of providing Mac devices to remote workers was challenging. The devices had to be set up prior to being shipped and, once received, remote users had to establish a direct connection to the corporate network via VPN to complete the enrollment process. With the new Mac Cloud Agent, the enrollment process is drastically simplified. Once the agent is deployed on the device, users can immediately log in with their existing credentials and complete the enrollment process without being connected to a VPN or corporate network.
The new Mac Cloud Agent also simplifies macOS endpoint management. You can group your Mac devices and define global access permissions, which automatically provides specific groups, roles, or users the ability to access and manage Mac endpoints enrolled into the Idaptive platform.
Some of the policies and actions you can take to secure enrolled Mac devices include:
- Lock device: prevent the end-user from unlocking the device without an administrator-provided security code.
- Wipe device: remotely wipe the device of all the stored data and reset it to factory settings in case the device is lost or compromised.
- Enforce FileVault disk encryption: remotely enforce macOS built-in disk encryption to ensure that device hard drive can’t be mirrored if the device is lost or stolen.
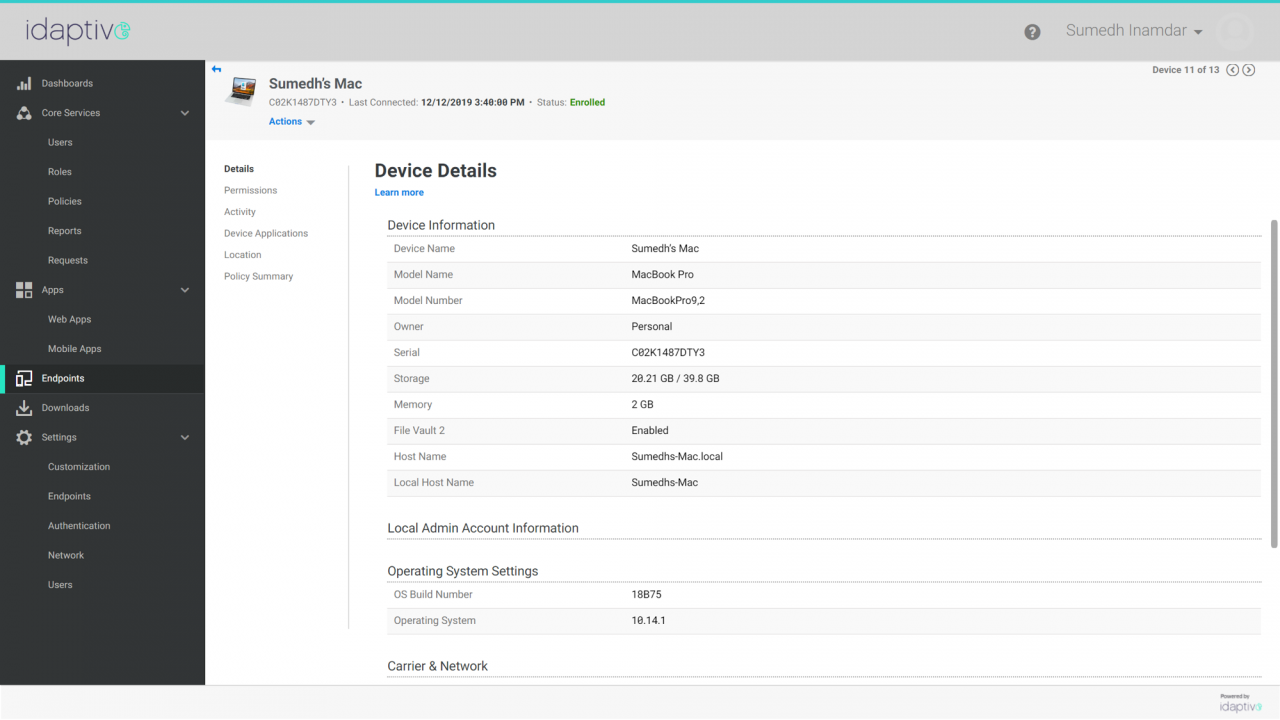
The Mac Cloud Agent also gathers device-level information, such as device name, model, OS settings, and location for each of the enrolled Mac machines. You can use this information to get better visibility into the security posture of your devices or to create conditional access policies.
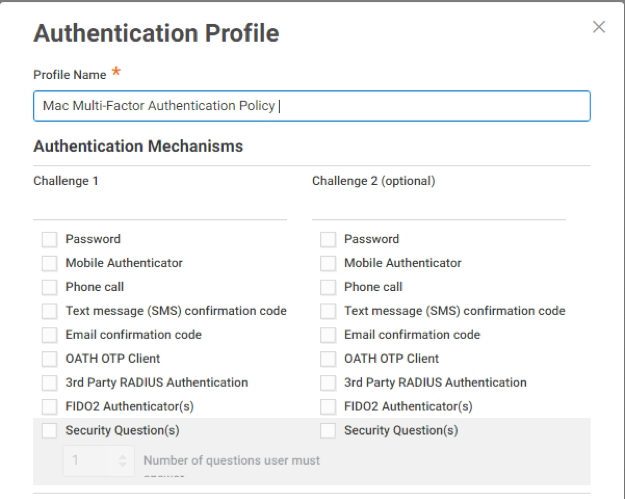
The Mac Cloud Agent also helps you to improve the overall company security posture by enabling the Adaptive Multi-Factor Authentication on enrolled Mac devices. Most of the corporate endpoints, including your Mac computers, contain sensitive information, such as company data, emails, and cached passwords and cookies. Endpoints can also serve as a launching point for security breaches by exposing access to services assigned to end-users. The Mac Cloud Agent enables you to take an extra step to ensure your Mac devices can’t be compromised by requiring users to pass secondary authentication challenges before access to endpoints is granted. For example, you can create a policy that requires users to pass two authentication challenges if the device is connected to a non-corporate network. The following screenshot shows a selection of authentication methods available for secondary authentication.
Lastly, the new Mac Cloud Agent can help improve the end-user experience by allowing access to certain applications without entering credentials. This capability is called Zero Sign-On (ZSO), and it is based on certificate-based authentication. The ZSO process is secure and convenient. Once the device is enrolled with the Idaptive platform, and the user is successfully authenticated into the device, ZSO-enabled applications can be accessed with a single click. However, you can always set up additional identity verification steps based on contextual factors, such as device location, IP address, and user behavior. For example, you can allow your employees to access applications from the corporate network without entering any credentials, and set up step-up authentication for accessing applications from outside.
2. What are the key features of Mac Cloud Agent?
Mac Cloud Agent includes the following key features:
Support for Domain credentials: You can use your corporate Active Directory or Idaptive Cloud Directory credentials to log in to your macOS devices.
Adaptive Endpoint MFA: With Mac Cloud Agent, you to require users to pass additional authentication challenges during the process of logging into their macOS. Adaptive Multi-Factor Authentication adds an extra layer of protection before access to endpoints is granted. Leveraging device, network, and user behavior context Idaptive intelligently assigns risk to each login request and allows you to create dynamic access policies that are triggered when anomalous behavior is detected.
Multi-Factor Authentication Grace Period: The Multi-Factor Authentication grace period configuration enables you to define a temporary window during which successfully authenticated users can continue to login to their devices with only their directory credentials, even if the authentication profile requires additional factors for authentication.
Offline OTP: With offline one-time-passcodes (OTP), you can sign in to your devices protected by Multi-factor Authentication even when you are not connected to the internet. Offline OTP setup is easily accessible directly in the agent drop-down menu and supports all standard OTP authenticator applications.
Mac Application Management: The application management capabilities leverage Munki, an open-source management tools specifically designed for the macOS platform, and allow you to deploy applications, update applications, and add both pre and post-install scripts.
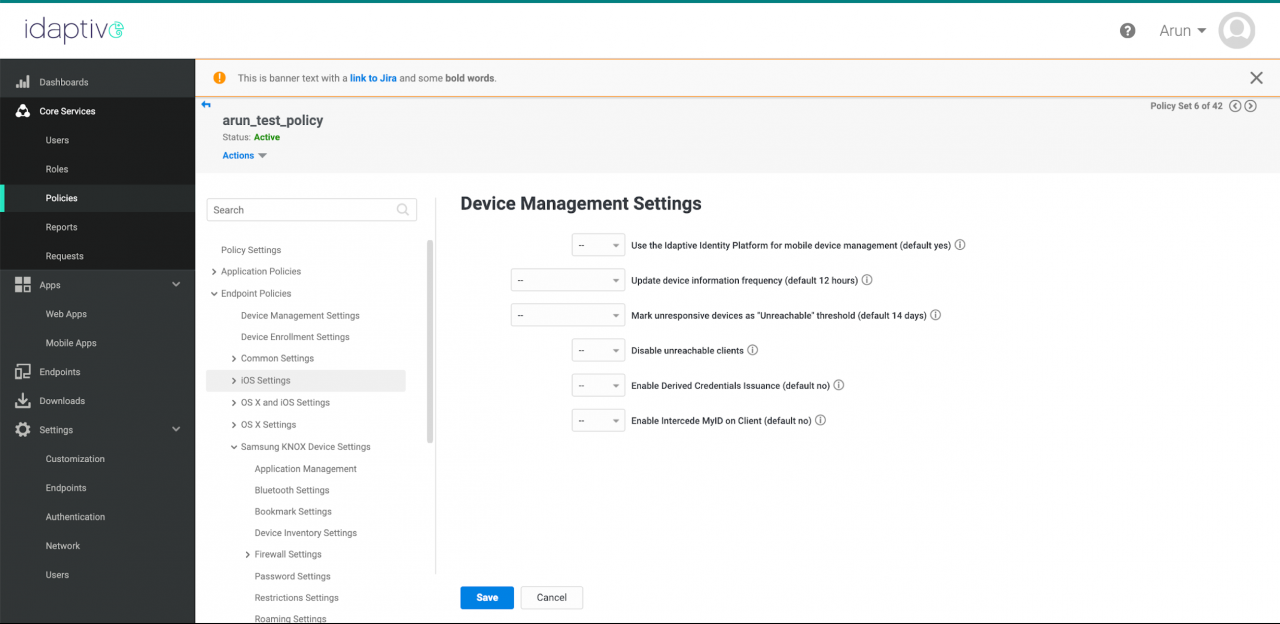
MDM features: the new Mac Cloud Agent supports over 15 policy settings including, enabling and disabling the macOS firewall, defining password complexity requirements, and controlling security and privacy group policies. You can find the complete list of Mac policy settings here.
3. How do I get started?
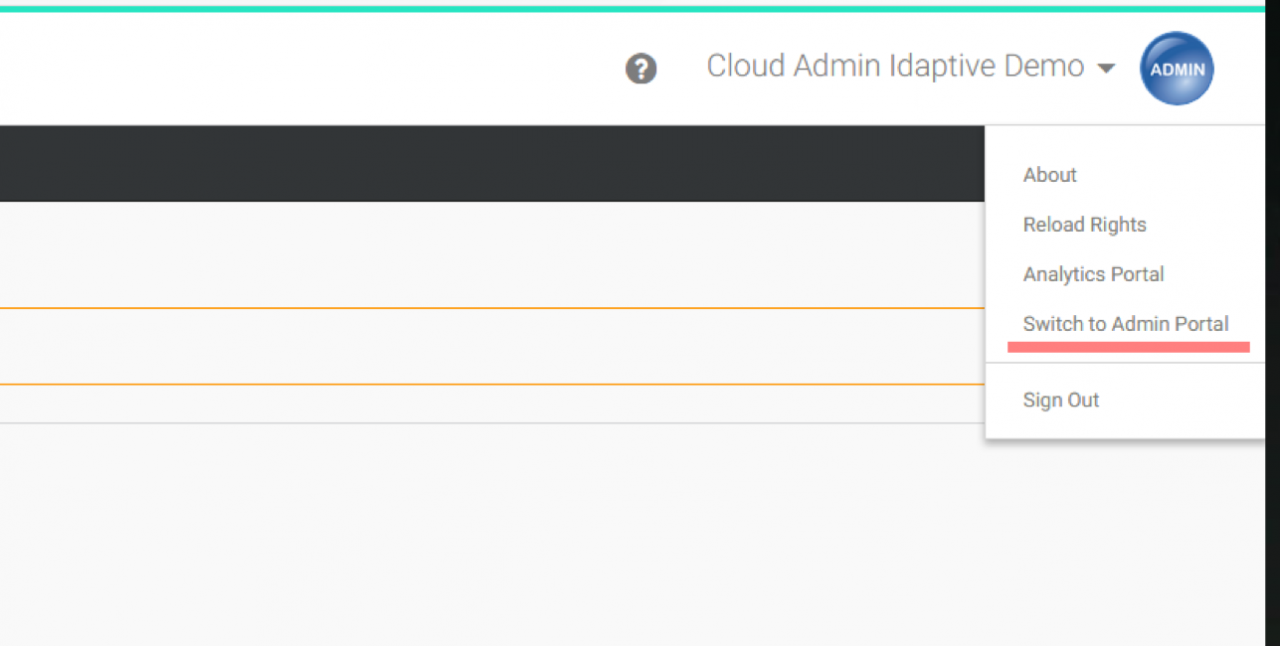
To get started, log into your Idaptive Portal as an Administrator and switch to the Admin Portal interface.
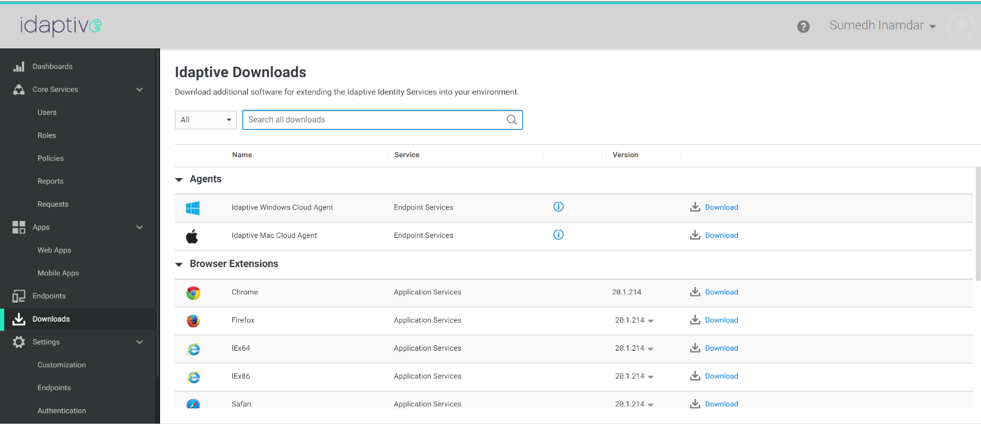
Once in the Admin Portal, navigate to the Download section on the left side of the menu. Here you’ll find the download link for the new Idaptive Mac Cloud Agent. Please note, you may need to request the Idaptive support team to enable this link for your Idaptive tenant if you don’t see it as a download option.
After downloading the Mac Cloud Agent, refer our help documentation to enroll a macOS device and assign a test user to the workstation.
Then, you can define an endpoint authentication policy, which in turn uses a suitable authentication profile for that user or role. You can use almost all of the existing authentication factors and authentication rules supported by the Idaptive User Portal to configure an Adaptive MFA login to your enrolled Macs.
Summary
In this blog post, I introduced the new Mac Cloud Agent and explained its key features, benefits, and use cases. With Mac Cloud Agent, you can centrally enroll and manage mac endpoints, secure endpoints with Multi-Factor Authentication, and enforce device-level policies. To start using Mac Cloud Agent, simply log in to your Idaptive tenant and download the agent on to your Mac device.


